Boolean World
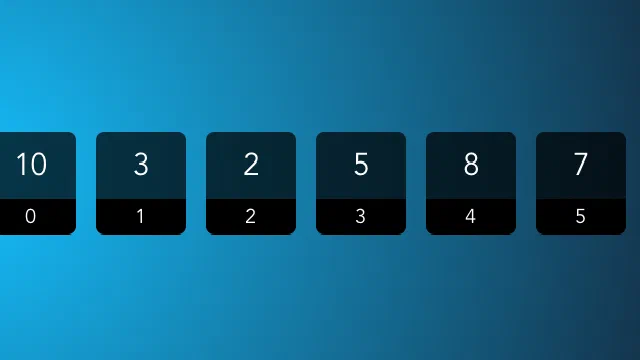
Arrays in C allow you to store multiple items of the same data type, such as a list of integers. Arrays can be to store a fixed number of items of the same data type under a single name.

As a Linux administrator, it is essential to know how to add users, modify users and delete users in a Linux system. It is a good practice to have different accounts for different …
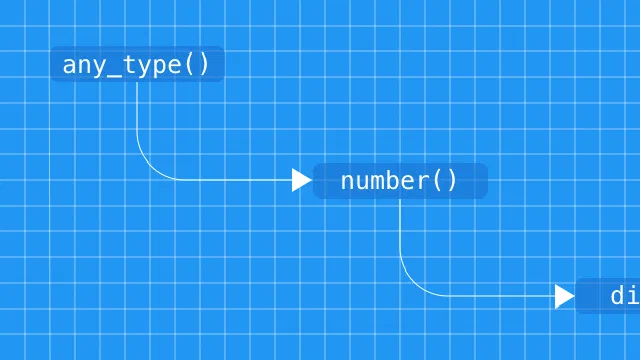
Parsers are programs that help process text. Compilers and interpreters use parsers to analyze programs before processing them further, and parsers for formats like JSON and YAML …

SSH (Secure SHell) is a network protocol that allows you to securely execute commands on and transfer files to a remote server. Typically, most servers running SSH are configured …

cURL is a command line tool and a library which can be used to receive and send data between a client and a server or any two machines connected over the internet. It supports a …

There are many different virtualization technologies available in the market, such as OpenVZ, KVM and Xen. You may have come across these terms when trying to while trying to buy …

The wget command allows you to download files over the HTTP, HTTPS and FTP protocols. It is a powerful tool that allows you to download files in the background, crawl websites, …

In an operating system, there are many programs, which may be either run by an user or by the OS itself (such as system services). Such programs which are running on the system …
The find command allows users to search for files and take actions on them. It is part of the “findutils” package and comes bundled with all distributions. It is …
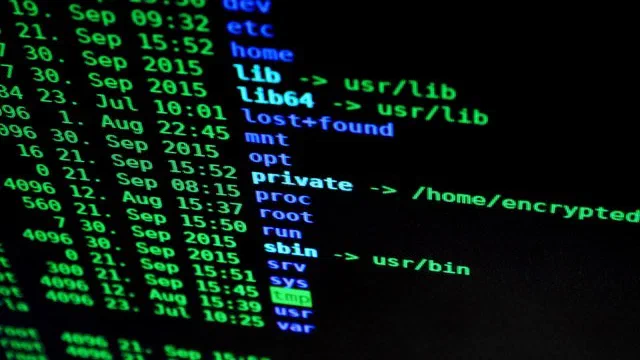
Linux is a multi-user operating system, and it ensures the security of files with the concepts of “ownership” and “permissions”. You can use these concepts …

Monitoring a system is essential for keeping things running smoothly. Glances is a Python-based tool which provides information on various aspects of the system, such as running …

Monitoring is an essential part of managing infrastructure. It helps you to ensure that your business keeps running smoothly, by alerting you to problems as they occur. Nagios is …

As businesses grow, demand arises for more reliable infrastructure that can handle critical systems. An important component in stable and scalable infrastructure is proper memory …

Monitoring is an important part of managing applications deployed on servers. They help you ensure applications run smoothly, as well as troubleshoot any problems that may arise. …

Developers and sysadmins may need to monitor various network parameters, such as bandwidth consumption and the traffic flowing in/out. There are many tools available for this …

Files placed on a web server are publicly accessible by default. If you want to protect files from unauthorized access, you can make use of HTTP basic authentication. It is a …
Fragmentation has been a problem for quite some time in the Linux ecosystem. A variety of distributions exist today, with their own package managers and their own notions of what …
Docker has changed the way developers run, organize and deploy their code and infrastructure. In the docker series articles, we will be understanding how Docker works, …

The top command allows users to monitor processes and system resource usage on Linux. It is one of the most useful tools in a sysadmin’s toolbox, and it comes pre-installed …
For very small websites, a single server running a web application is usually enough. However, this doesn’t work well for larger websites. In such cases, we make use of …